If you’re in the business of defense contracting, like many clients we partner with at Mainstay Technologies, you’ve likely heard the acronym “CMMC” this year! Whether we’ve met you at a workshop or seminar on security and compliance, or you’re just starting to evaluate what level of CMMC you need to meet, we’re here to guide you through compliance assessments and navigating next steps. But let’s start at the beginning: how we arrived at this new cybersecurity certification requirement.
The first question we typically hear is about how regulations established in recent years for defense contractors, like DFARS and NIST, fit in with CMMC. Are you choosing between existing compliance and CMMC certification? The simple answer is no because prior compliance regulations have been neatly nested into the CMMC framework. It serves as an evolution of the initial cybersecurity demand put out for similar reasons—protecting federal contract information and controlled unclassified information that are vulnerable in the Department of Defense supply chain. Those that operate in the Defense Industrial Base sector are increasingly targeted by cyber-attacks due to this sensitive information. For many organizations in the DoD supply chain, NIST SP 800-171 and 800-53 were initial frameworks used to establish security standards for federal information security.
The NIST SP 800-171 standard presents a unique challenge in that a self-assessment of the 110 controls is the requirement compared to CMMC where an accredited audit will be required based on your level 1-5 (basic through advanced) security as detailed below. There was a critical need to build in that accountability to protect federal information. CMMC compliance should be seen as a positive evolution that is needed to safeguard DoD CUI and your business. We’ve outlined below the basic framework, what it means for you and your company, and next steps.
What is CMMC and why should my company seek compliance?
CMMC Version 1.0 was released in January 2020 and serves as a unified cybersecurity standard for future Department of Defense (DoD) acquisitions. For the bidding process on DoD contracts, CMMC will ensure a fairer process by outlining required levels based on your company’s business requirements. CMMC V1.0 defines a maturity model as a set of characteristics, attributes, indicators, or patterns that represent capability and progression in a particular discipline. It works to establish best practices through defining and structuring action that must be taken by a company to prove that it has incorporated these practices.
The maturity processes formalize cybersecurity activities to ensure they are consistent, repeatable, and high quality. It offers guidance so that all companies are clear on what is required at each level, creating an even playing field for contractors and subcontractors. The CMMC practices provide a range of mitigation across the levels, starting with basic safeguarding, moving to the broad protection of controlled unclassified information, and culminating with reducing the risk of advanced persistent threats. The framework offers clarity on how to achieve levels of cybersecurity, it is coupled with a certification program to verify the implementation of these processes and practices.
Companies that seek to create and supply products that support U.S. military operations, as contracted through the DoD will be required to meet certain levels of cybersecurity maturity, evidenced by the CMMC certification. Companies will coordinate directly with an accredited and independent third-party auditing organization to become CMMC certified. Through this process, the company would request a specific level of certification based on what they do within the supply chain.
To prepare for the third-party audit and maintain CMMC certification, companies are encouraged to work with a partner, like Mainstay Technologies, which has the ability to conduct readiness assessments, remediate findings, and maintain your authority to operate. Engaging in this level of preparation, assessment, and remediation before you work with an auditor can be critically important to your intended outcome.
The CMMC Framework
The CMMC model framework organizes processes and cybersecurity best practices into a set of domains. For each of the 17 domains, there are processes that span five levels of cybersecurity maturity. Additionally, each of the domains contain one or more capabilities spanning the five levels. And, for a given capability, there are one or more practices that must be demonstrated.
The 17 Domains
Each domain is comprised of processes and capabilities across the five levels. The domains include:
- Access Control (AC)
- Asset Management (AM)
- Awareness and Training (AT)
- Audit and Accountability (AU)
- Configuration Management (CM)
- Identification and Authentication (IA)
- Incident Response (IR)
- Maintenance (MA)
- Media Protection (MP)
- Personnel Security (PA)
- Physical Protection (PE)
- Recovery (RE)
- Risk Management (RM)
- Security Assessment (CA)
- Situational Awareness (SA)
- System and Communication Protection (SC)
- System and Information Integrity (SI)
The 5 Levels of Cybersecurity Maturity
As a company seeks to progress the levels, each level is cumulative and must be fully compliant in order to achieve a greater level of maturity. Some existing DoD compliance requirements governing Controlled Unclassified Information (CUI) are integrated within the levels below, where appropriate. If your company complies with NIST SP 800-171, for example, more detail can be found at Level 3.
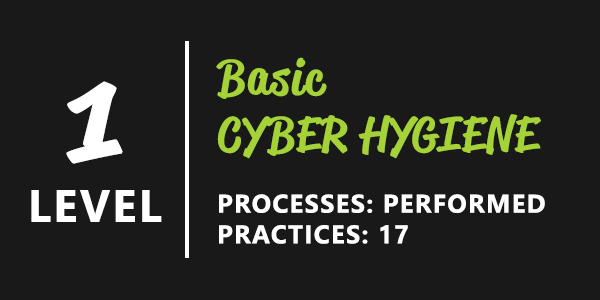
Processes are performed and select practices are documented where required. There are 17 practices to demonstrate basic cyber hygiene. Equivalent to all practices in Federal Acquisition Regulation (FAR) 48 CFR 52.204-21 from FAR Clause 52.204-21. The first level ensures basic safeguarding of federal contract information.
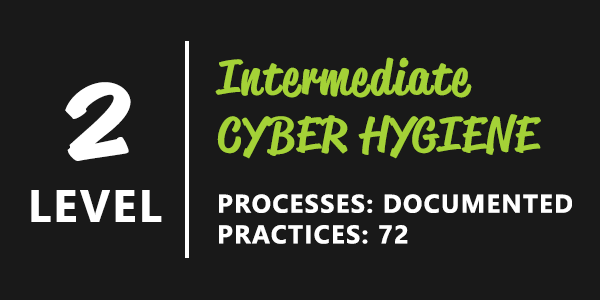
Processes are documented, including Level 1 practices and a policy exists that includes all activities. Practices demonstrate intermediate cyber hygiene. This level complies with FAR, includes a select subset of 48 practices from NIST SP 800-171, and includes an additional 7 practices to support intermediate cyber hygiene. A total of 72 practices must be demonstrated at this level as organizations transition to demonstrate cybersecurity maturity progression to protect controlled unclassified information.

Processes are managed and documented including all lower levels. A policy exists that covers all activities and a plan exists, is maintained, and resourced that includes all activities. This level complies with FAR and encompasses all practices from NIST SP 800-171, and includes an additional 20 practices to support good cyber hygiene. A total of 130 practices are needed to demonstrate this level as organizations protect controlled unclassified information.
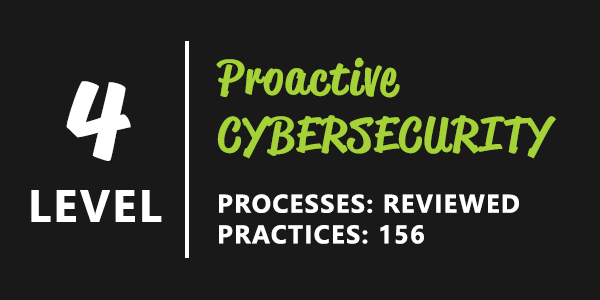
Processes are reviewed, and each practice is documented, including lower levels of cyber hygiene. With 156 practices, this level demonstrates proactive cyber hygiene. Policies and plans exist that cover all activities. Additionally, activities are reviewed and measured for effectiveness and results are reported to higher-level management. This level complies with FAR and encompasses all practices from NIST SP 800-171, and a select subset of 11 practices from Draft NIST SP 800-171B. This level includes an additional 15 practices to demonstrate a proactive cybersecurity program. This level, and beyond, protect CUI as well as reduce risk from advanced persistent threats.
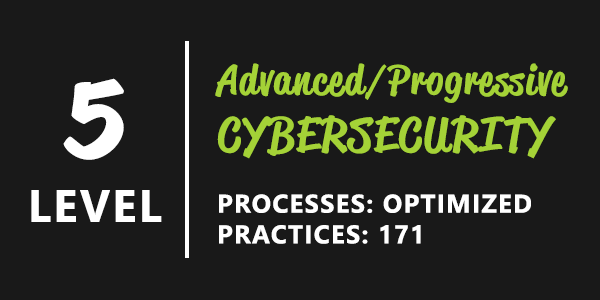
Processes are optimized, and each practice is documented, including lower levels of cyber hygiene. Policies and plans exist that cover all activities, and activities are reviewed and measured for effectiveness. At this high level of cybersecurity, a standardized, documented approach across all applicable organizational units is evident. With 171 total practices, this level complies with FAR and encompasses all practices from NIST SP 800-171, and a select subset of 4 practices from Draft NIST SP 800-171B. This level includes an additional 11 practices to demonstrate an advanced and progressive cybersecurity program.
Timeline and what’s next
Beginning in 2020, the DoD will train third-party auditors and certifying bodies for CMMC. Ellen M. Lord, Under Secretary of Defense for Acquisition and Sustainment (A&S), shared during a news conference announcing the certification that a series of CMMC third-party auditor organizations (C3PAOs) will conduct the audits for those seeking certification. A 13-member CMMC Accreditation Body is being established to oversee training, quality, and administration of the C3PAOs. You can read more from the news conference here.
Today, you can start working with a partner like Mainstay Technologies for readiness assessment to prepare for what comes next. By June, the DoD plans to publish as many as 10 requests for information on contracts that include CMMC requirements at a mix of levels according to defense.gov. Note that CMMC requirements will not be inserted into any existing contracts. Additionally, by fiscal year 2026, all new contracts from the DoD will include the CMMC requirements. Subcontractors and contractors will not need to have the same level of certification to win a contract.
Mainstay Technologies has been working in this field for several years and has built up the necessary expertise to serve as a trusted partner to perform compliance assessments, identify real world risk factors, remediate any findings, and carry the overall responsibility for cybersecurity long-term. Prior to your third-party audit, we would look forward to working with you on assessing your compliance levels and any areas for remediation. Reach out and see how we might work together.

